So BTP launched this new app called ASTRAM. Big deal in Bangalore everyone was downloading it to check fines, traffic updates, all that. The app was built by Arcadis, which is like a massive multinational company. Not some random startup.
I downloaded it too. But old habits die hard I fired up Proxyman to see what’s going on under the hood.
Wait, What?
First thing I noticed: HTTP. Not HTTPS. In 2025. For an app that handles traffic violations and citizen data.
That’s already a red flag. But I kept digging.
The API requests were… interesting. I could see stuff in the responses that wasn’t showing up in the app UI. Like, the app shows you your violation details, but the raw API response was sending back way more addresses, personal info, things that shouldn’t be leaking.
And the authentication? Let’s just say if you were on the same WiFi as someone using this app, you could see things you shouldn’t.
I Tweeted
Look, I’m not trying to be a hero here. But this was a government app for a city of 13 million people built by a company with 36,000 employees. This shouldn’t slip through.
Found some concerning security issues in the new BTP ASTRAM app on launch day. Reported responsibly. @BlrCityTraffic
— Ashutosh Shukla (@ashu_shukla_) March 29, 2025
I kept it vague on purpose. No exploit details, no screenshots of the actual vulnerabilities. Just flagged that something was wrong.
The Joint CP Reached Out
Few hours later, I get a DM request from a verified account Joint Commissioner of Police, Traffic, Bengaluru. 144K followers. Official blue tick.
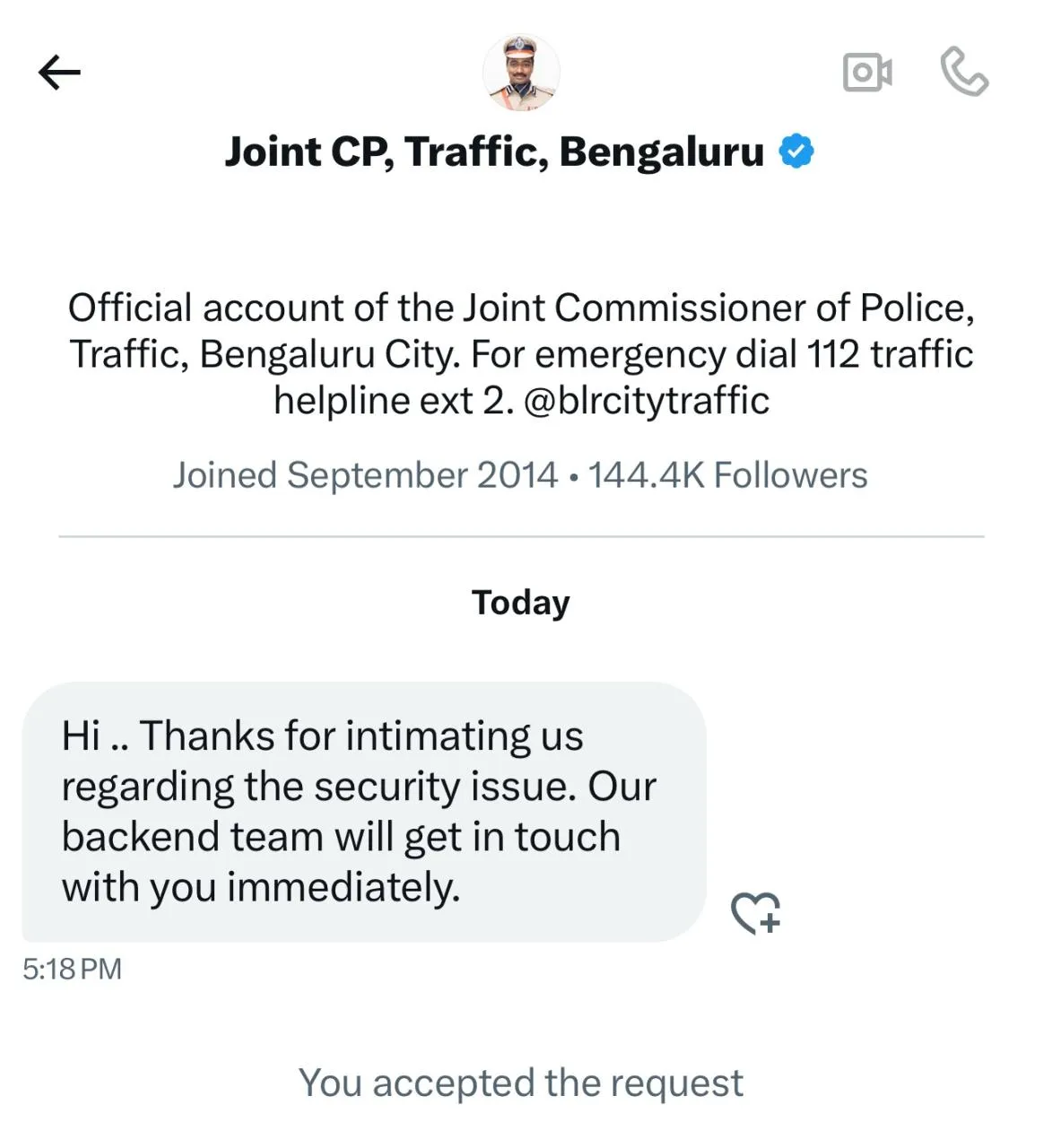
“Hi.. Thanks for intimating us regarding the security issue. Our backend team will get in touch with you immediately.”
I shared the exact details with their team what was exposed, how to reproduce it, and what needed fixing.
They Fixed It
Backend team got on it. Issues patched.
And honestly? That felt good. Not because I got noticed or whatever but because the system actually worked. Found something sketchy, reported it properly, and it got fixed before anyone could misuse it.
The Point
I’m not a professional security researcher. I just have a habit of running Proxyman on new apps. Sometimes you find nothing. Sometimes you find… this.
If you spot something, report it. Don’t exploit it, don’t post the details publicly. Give them a chance to fix it first. Most orgs will appreciate it.
Some might even slide into your DMs.
Vulnerability details intentionally kept vague. It’s been fixed.
Questions about API security or want to chat? Hit me up.
